For 200 consecutive weeks, Threat Insights has analysed real‑world cyber threats facing European organisations. To mark the milestone, we revisited the archive to identify the five most‑read articles — revealing the attack techniques, risks, and visibility gaps security teams care about most.
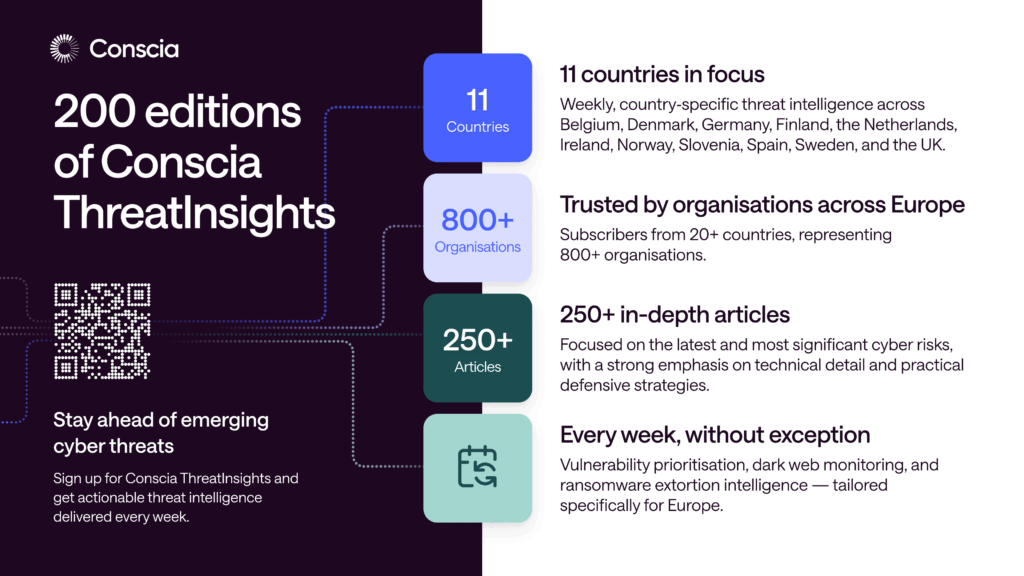
For 200 consecutive weeks, we have published ThreatInsights – our weekly, European‑focused newsletter sharing real‑world cybersecurity threats, how they work, and what defenders need to pay attention to.
Reaching 200 editions is not just a numerical milestone. It represents four years of continuous threat monitoring, analysis, and knowledge sharing with security professionals across industries. To mark the occasion, we searched the archive and identified the five most‑read articles featured in ThreatInsights.
Together, they provide a telling snapshot of the security concerns that matter most to our readers — and of the threat landscape organisations are navigating today.
The five most‑read ThreatInsights articles
- Diving deep: How to detect typosquatting
Typosquatting is a deceptively simple technique that continues to be highly effective. This article explores how threat actors register look‑alike domain names to impersonate legitimate organisations, distribute malware, or harvest credentials — and how defenders can proactively identify these domains before they are abused.
Its popularity highlights strong interest in early‑stage threat detection and in defending against attacks that often bypass traditional security controls by exploiting user trust rather than technical vulnerabilities.
Read how to detect typosquatting and malicious look‑alike domains
- Diving deep: Malware injection techniques
Malware injection techniques are fundamental to how modern malware evades detection. This article explains why signature‑based security struggles against today’s threats and how attackers abuse legitimate processes to execute malicious code.
It offers technical insight into attacker tradecraft, going beyond what malware does to explain how it achieves execution and persistence in increasingly hostile defensive environments.
Explore common malware injection techniques and attacker tradecraft
- Vulnerability spotlight: How to detect Follina (Windows MSDT zero‑day)
When the Follina vulnerability (CVE‑2022‑30190) emerged, it quickly became an actively exploited zero‑day. This article focuses on the mechanics of the vulnerability and, crucially, how exploitation can be detected across different delivery methods — not just a single attack scenario.
It provided actionable detection guidance at a time when immediate patching or mitigation was not always feasible.
Learn how to detect exploitation of the Follina Windows MSDT zero‑day
- Digital forensics: Discovering threat actors’ traces using the Recycle Bin
This article demonstrates how seemingly mundane artefacts — such as the Windows Recycle Bin — can provide valuable forensic evidence during incident response. It shows how attackers often unintentionally leave traces and how these can help reconstruct attacker activity.
What resonates is the emphasis on forensic visibility and investigation — understanding what happened after access was gained, and how small details can make a critical difference.
See how Windows Recycle Bin artefacts support digital forensics
- The OpenClaw security crisis
This article examines a large‑scale security issue rooted in exposed management interfaces and poor security hygiene, illustrating how systemic weaknesses can create widespread risk. Rather than focusing on a single vulnerability, it highlights how misconfigurations and exposure can be exploited at scale.
It reflects growing concern about structural and operational security risks, where the issue is not a missing patch, but how systems are designed, exposed, and managed.
Understand the OpenClaw security crisis and large‑scale exposure risks
What is ThreatInsights?
ThreatInsights is Conscia’s weekly cybersecurity newsletter, delivering concise, technically grounded analysis of emerging threats, vulnerabilities, and real-world incidents, with a special focus on Europe.
Each edition is designed to help security leaders and practitioners stay informed about how attacks unfold in practice, what to look for from a detection and response perspective, and how the threat landscape is evolving — without hype or speculation.
Two hundred weeks on, the mission remains unchanged: to provide clarity, context, and practical insight in a constantly shifting security environment.
CONTACT
The author behind the newsletter
A special thank you to David Kasabji, the main author of ThreatInsights, whose consistency, technical depth and sharp analysis have been at the heart of the newsletter from the very beginning.
Week after week, David’s work helps our readers understand how threats really work.
